Original Posting can be found here
Setting up an OpenVPN server with Ubiquiti EdgeRouter (EdgeOS) and Viscosity
Virtual Private Networks (VPNs) can be utilized for a number of very useful applications. You can securely connect to any public WiFi hotspot. You can overcome geo-blocking restrictions on your favourite websites. And you can even connect to your home or office network from anywhere in the world, as if you were sitting right at your desk. This guide will walk you through the process of setting up your own OpenVPN server, and connecting to it with your copy of Viscosity.
Running your own OpenVPN server will allow you to encrypt everything you do on the internet, so that you can safely do your online banking on the free WiFi at your favourite cafe. Anything you send over the VPN connection will be encrypted from your device until it reaches your OpenVPN server at home. Setting up your OpenVPN server to access your home or office network gives you full access to all your files on your network.
This guide will walk you through the steps involved in setting up an OpenVPN server on Ubiquiti EdgeRouter (EdgeOS) that allows you to securely access your home/office network from a remote location and optionally send all of your network traffic through it so you can access the internet securely as well. This guide was written using a Ubiquiti EdgeRouter Lite, but should work with any Ubiquiti device running EdgeOS v1.9 or later.
This guide won’t treat any issues related to setting up your router. A router running EdgeOS is likely to be acting as a router itself, so we will assume that the Ubiquiti EdgeRouter is directly connected to the internet with its own IP address.
Preparation
For this guide, we assume:
- You have an already functional Ubiquiti EdgeRouter running EdgeOS (also known as “EdgeMax Software”) v1.9 or later.
- Your router has been setup with at least one WAN and one LAN interface
- You are connected with your Ubiquiti EdgeRouter via a LAN connection.
- Only the initial setup wizard for setting up your router with a WAN and LAN interface has been run.
- You already have a copy of Viscosity installed on your client device
Further information on Ubiquiti EdgeRouter and EdgeOS products can be found at https://www.ubnt.com/broadband/#edgemax. Product updates for your router can be found at https://www.ubnt.com/download/. If you are looking to setup an OpenVPN server on a different operating system, please check out our other guides.
If you don’t have a copy of Viscosity already installed on your client, then please check out this setup guide for installing Viscosity (Mac | Windows).
Support
Unfortunately we cannot provide any direct support for setting up your own OpenVPN server. We provide this guide as a courtesy to help you get started with, and make the most of, your copy of Viscosity. We’ve thoroughly tested the steps in this guide to ensure that, if you follow the instructions detailed below, you should be well on your way to enjoying the benefits of running your own OpenVPN server.
For further information or help with your Edgerouter, check out the community forums at https://community.ubnt.com/t5/EdgeRou…/EdgeMAX
Getting Started
We will assume that you have already set up your network interfaces as such:
- ‘Internet’ – eth0 or pppoe0 connected to the internet
- ‘Local’ – eth1 connected to your local home network
Generating Certificates and Keys
The next step is to generate your configurations for the server and your clients as well as certificates to go with them. You can do this easily by following the Creating Certificates and Keys Guide. Generate everything on your PC or Mac and then take a note of the path to your server folder that is created, we will be using the files here later on.
If you use the default DNS Server (10.8.0.1), you will need to setup a DNS server yourself, instructions are at the end of this article. We recommend instead using an existing DNS server, a publically available DNS server like Google’s (8.8.8.8 and 8.8.4.4) is the easiest.
We now need to copy the following files to the /config/auth/ directory on your Edgerouter which will be in the server folder that openvpn-generate just created, we recommend using SCP. If you’re unfamiliar with SCP, we have some help on how to transfer files with SCP in our Introduction Guide.
- ca.crt
- server.crt
- server.key
- dh.pem
If you’re using SCP from command line, an example command would bescp path/to/server/ca.crt ubnt@router-address:/config/auth/
OpenVPN Server Configuration
At the time of writing, EdgeOS does not include a GUI interface for setting up an OpenVPN server like it does for other VPN protocols. Fortunately however, all the tools are available on the router to be able to easily configure an OpenVPN server via command line.
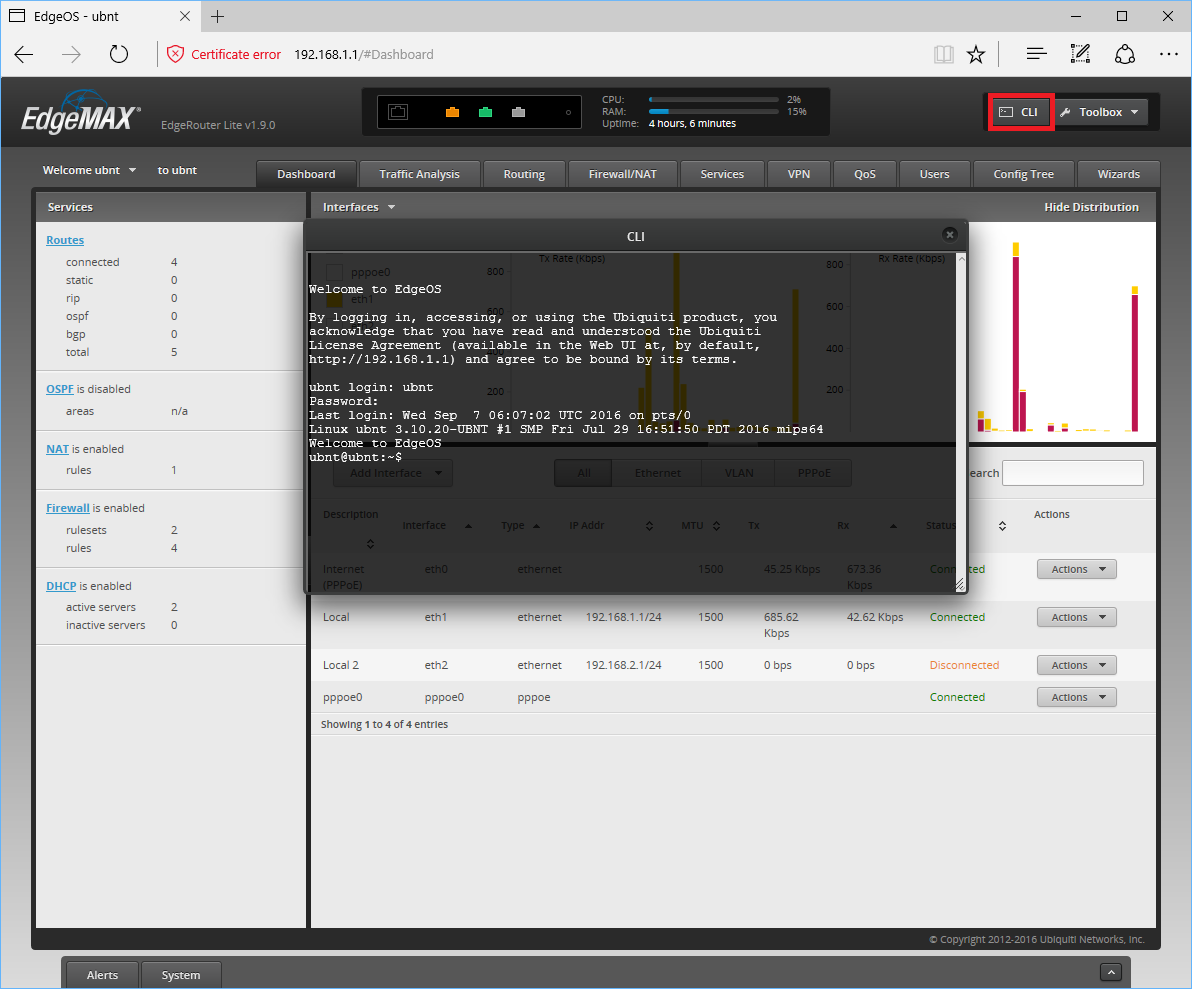
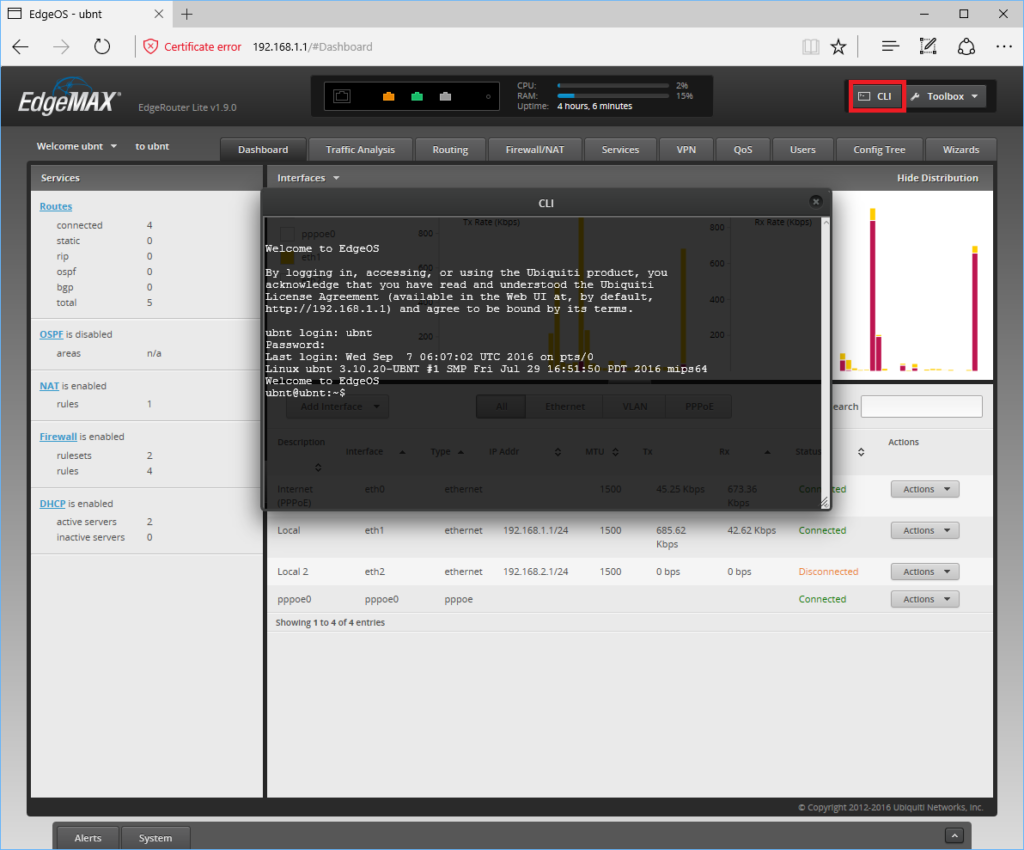
You can access the command line interface of your router in multiple ways. For the purpose of this guide we will be using the command line interface included in the web portal. To access this, open a web page and navigate to the IP Address of your EdgeRouter device (https://192.168.1.1 by default). Login, then click the CLI button towards the top right hand corner of this page. This will open a black background CLI window in your browser. You can login to this using the same details you used to login to the EdgeOS web page.
For more advanced users, this guide can also be followed by accessing the device via Console or SSH.
There are a number of different settings we need to customize in our OpenVPN server configuration. In the terminal, enter configuration mode by typing:
configure
You should see the prompt change from $ to #. If you make a mistake entering the following configuration commands, you can remove a previously entered command by repeating the it, but replacing the word ‘set’ at the start with the word ‘delete’.
Paste the following into the terminal window:
# Configure this OpenVPN instance to run as the VPN server set interfaces openvpn vtun0 mode server # The OpenVPN server needs to know the location of the Diffie Hellman file #NOTE: Depending on how you generated your keys, this file name might be 'dh.pem' instead set interfaces openvpn vtun0 tls dh-file '/config/auth/dh.pem' # Our VPN connection will be transported over UDP set interfaces openvpn vtun0 openvpn-option "--proto udp" # The server needs to keep a record of client virtual IP addresses so that they # can be reassigned if the server goes down set interfaces openvpn vtun0 openvpn-option "--ifconfig-pool-persist ipp.txt" # To ensure that each side of the VPN knows if the connection has been severed, # we want to ping each side every 10 seconds. If either side fails to recieve a # ping within 2 minutes, then it will assume the other side is down set interfaces openvpn vtun0 openvpn-option "--keepalive 10 120" # There can be security issues if you run the OpenVPN server as root, so we will # downgrade the user and group set interfaces openvpn vtun0 openvpn-option "--user nobody --group nogroup" # To avoid attempting to access resources that may no longer be accessible on # restart set interfaces openvpn vtun0 openvpn-option "--persist-key --persist-tun" # To write (and rewrite) a short summary of current VPN connections every minute # to a file set interfaces openvpn vtun0 openvpn-option "--status openvpn-status.log" # The verbosity of this connection logging (displayed in the Viscosity 'Details' # window) can range from 0 (silent) to 9 extremely verbose. We will use the # default of 3 set interfaces openvpn vtun0 openvpn-option "--verb 3" # To prevent more than 10 duplicates of the same log message in a row from # flooding the Viscosity log set interfaces openvpn vtun0 openvpn-option "--mute 10" # The credential files set interfaces openvpn vtun0 tls ca-cert-file '/config/auth/ca.crt' set interfaces openvpn vtun0 tls cert-file '/config/auth/server.crt' set interfaces openvpn vtun0 tls key-file '/config/auth/server.key' # The server will use the default OpenVPN port (1194) set interfaces openvpn vtun0 openvpn-option "--port 1194" # We need the VPN to create a tun network interface through which we can # route all our traffic: set interfaces openvpn vtun0 openvpn-option "--dev vtun0" # The VPN requires a private IP subnet. We will use the default OpenVPN IP # subnet set interfaces openvpn vtun0 server subnet '10.8.0.0/24' # We want VPN clients connected to this server to be able to access any hosts # accessible on your home network. We are assuming that your local network # subnet is 192.168.0.x/24. If it is something else, you will need to change the # IP address in the command below. set interfaces openvpn vtun0 server push-route 192.168.0.0/24 #Set the OpenVPN server to push a DNS server to clients. This can be your local DNS #which we setup later, an external DNS of your choice, or you can omit this command #to setup DNS on the client only. set interfaces openvpn vtun0 server name-server 192.168.1.1 # For enhanced security, set a cipher and auth hash set interfaces openvpn vtun0 openvpn-option "--cipher AES-256-CBC" set interfaces openvpn vtun0 openvpn-option "--auth SHA256" # Lastly, we want to allow hosts on the home network to be able to see VPN # clients connected to the OpenVPN server set interfaces openvpn vtun0 openvpn-option "--client-to-client" #Save and end the configuration commit save exit
Pay special attention to the IP address in the set interfaces openvpn vtun0 server push-route 192.168.0.0/24. Ensure that this subnet matches your home/office LAN IP subnet. If you are not setting up this VPN server to access your home/office LAN, then you can skip this line altogether.
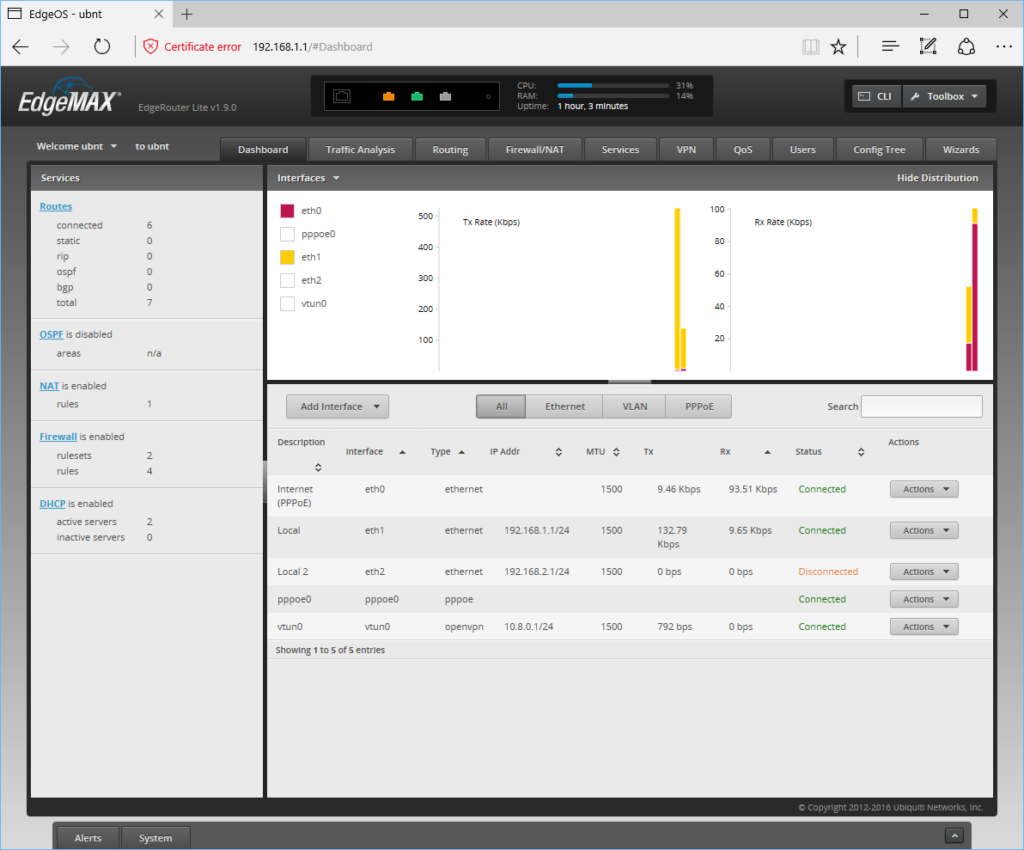
We are now done with command line, everything else can be done from the EdgeOS GUI via a web browser. Next, login to your route via your browser of choice, and you should see the new OpenVPN interface on the Dashboard.
Firewall Rules
If you are using the default firewall setup, we only need to set up a couple of things. First, we need to enable NAT masquerade for the VPN interface. To do this, open a web browser, navigate and login to your EdgeRouter device. Next, click the Firewall/NAT tab at the top of the window, then select the NAT tab that appears underneath. Click Add Source Nat Rule and configure the following options:
- Description – OpenVPN MASQ eth0
- Select “Use Masquerade”
- Select “All protocols”
- Outbound Interface – eth0
- Src Address – 10.8.0.0/24
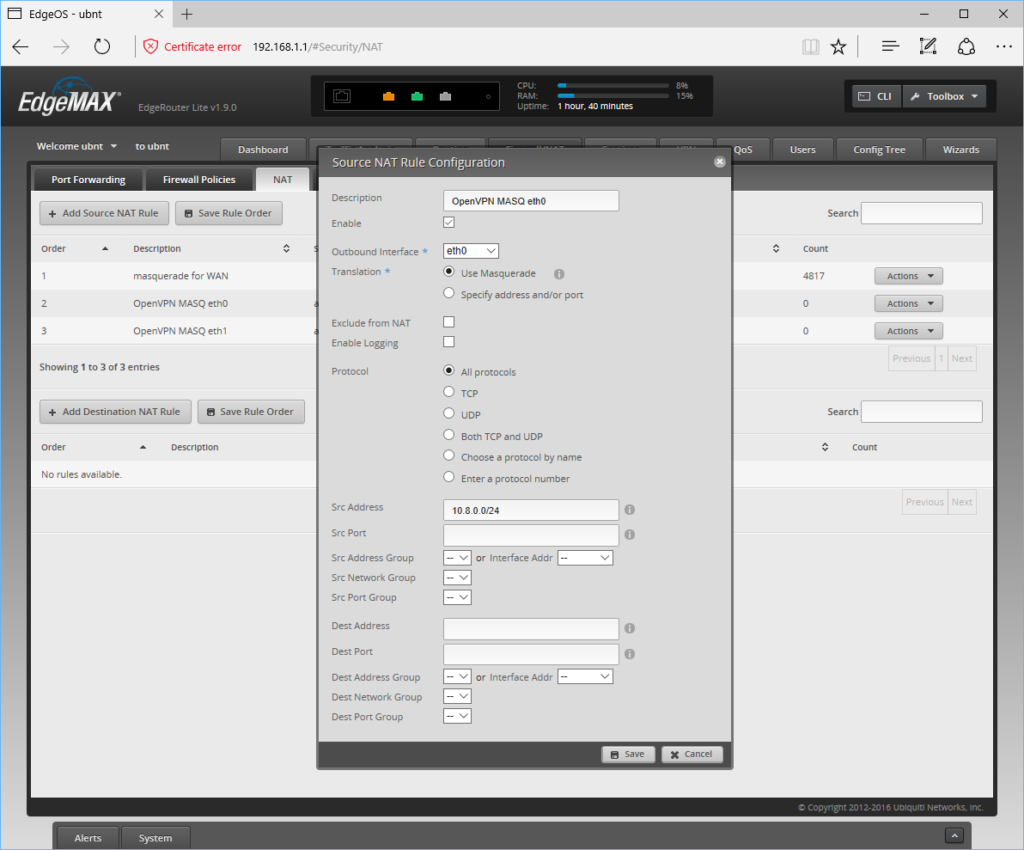
Then click Save. We need to add a rule for each interface we want OpenVPN clients to be able to communicate with, so at minimum we need to add one more. Click Add Source Nat Rule again and configure the following options:
- Description – OpenVPN MASQ eth1
- Select “Use Masquerade”
- Select “All protocols”
- Outbound Interface – eth1
- Src Address – 10.8.0.0/24
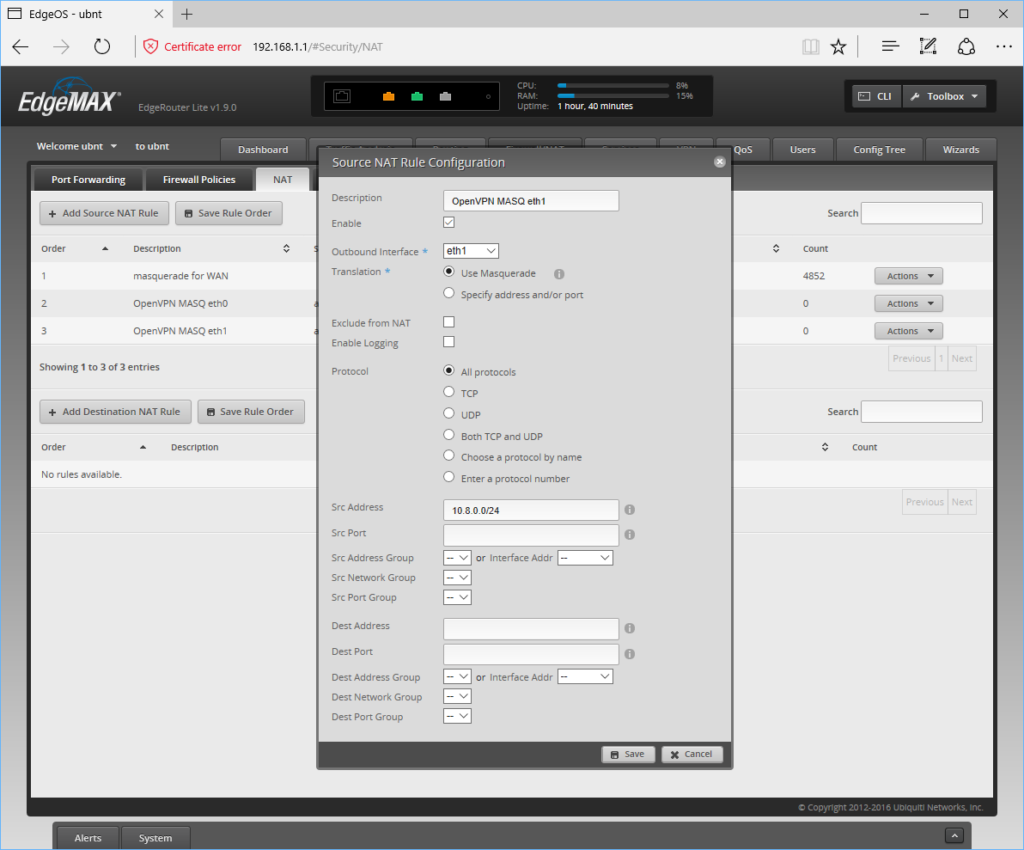
Then click Save.
Next we need to configure a firewall rule to allow us to connect to the OpenVPN server when we’re outside the local network, like on the road or at a coffee shop. To do this, click the Firewall/NAT tab, then click the Firewall Policies tab which appears underneath
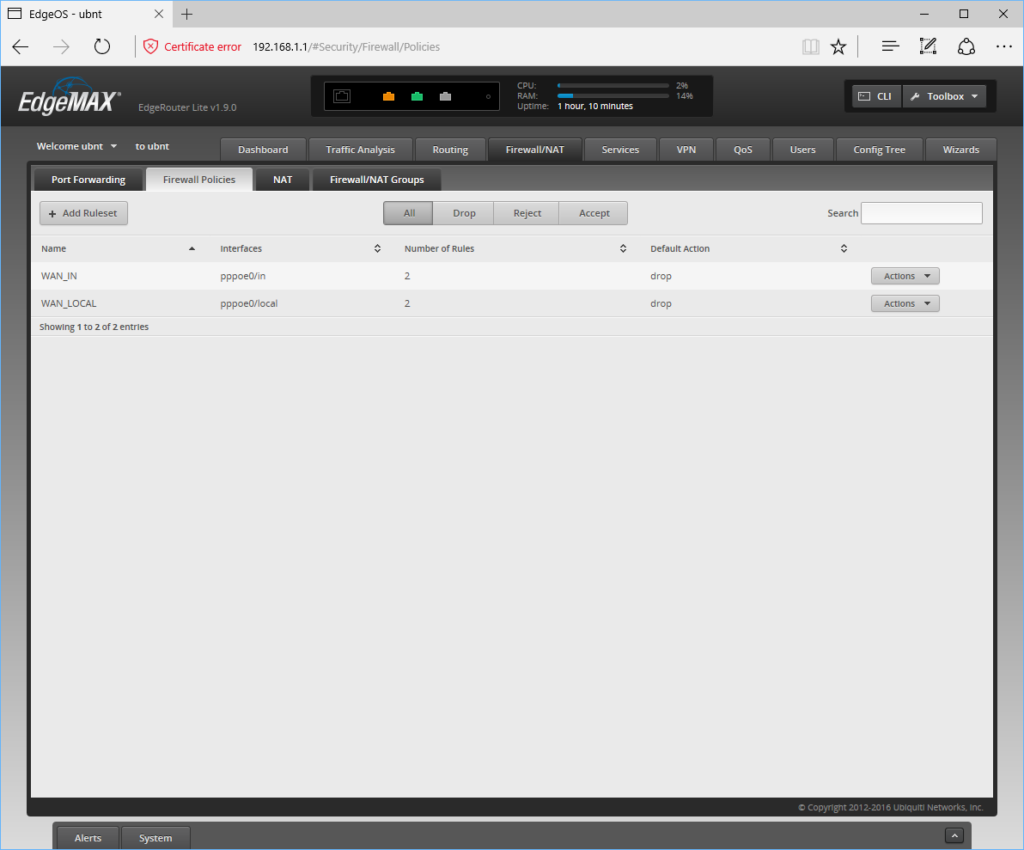
You should see a rule-set here named WAN_LOCAL. We want to add a new rule to this, so click Actions on the right and select Edit Ruleset. In the new window that appears, click Add New Rule and fill in the following details:
General Tab:
- Description – Allow external connections to OpenVPN
- Action – Accept
- Protocol – UDP
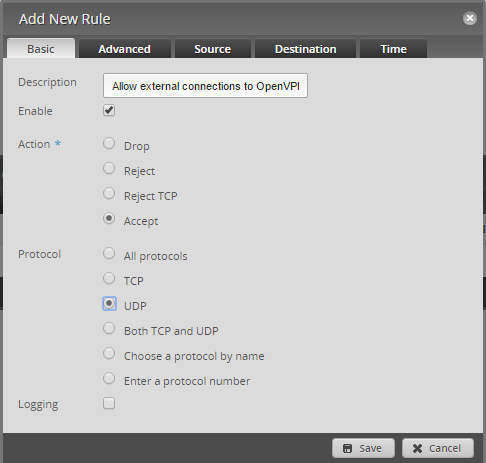
Destination Tab:
- Port – 1194
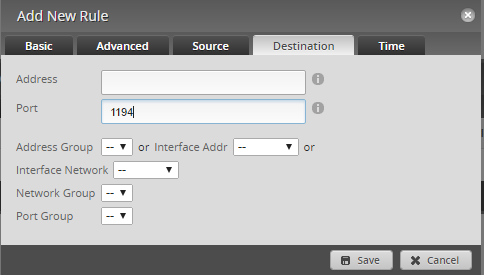
Click Save, then click Save Ruleset. You should now be able to connect to your OpenVPN server from an external location.
DNS Server
If you are planning on encrypting all network traffic through your VPN server then it is recommended to enable your own DNS server. EdgeOS has a DNS forwarder built in which we can use to provide our own DNS server for the VPN connection, to prevent DNS related attacks.
If your router is already setup for your local network (and you entered the command to use your router as DNS for OpenVPN), it is extremely easy to reuse your local DNS setup.
To do this, open a web browser, navigate and login to your EdgeRouter device. Click the Services tab, then click the DNS tab which appears underneath. Click Add Listen Interface, select vtun0 in the new drop down that appears, then click Save underneath.
Setting Up Viscosity
The final step is to setup Viscosity. Thanks to openvpn-generate, this is as easy as importing and connecting.
Importing
Copy your *.visz file you created with openvpn-generate to your Mac or Windows machine with Viscosity installed and double click the file. You should see a prompt that the config was imported successfully.
Once imported, edit your connection and go to the Advanced tab. Add the following two commands on new lines:
cipher AES-256-CBCauth SHA256
Then click Save to store these changes.
Connecting and Using Your VPN Connection
You are now ready to connect. Click on the Viscosity icon in the macOS menu bar or Windows system tray to open the Viscosity Menu, select the connection you imported, and Viscosity will connect.
To check that the VPN is up and running, you can open the Details window from the Viscosity Menu. This will allow you to view connection details, traffic and the OpenVPN log.

That’s it, you’ve set up your very own OpenVPN server. Congratulations, you are now free to enjoy the benefits of operating your own OpenVPN server!
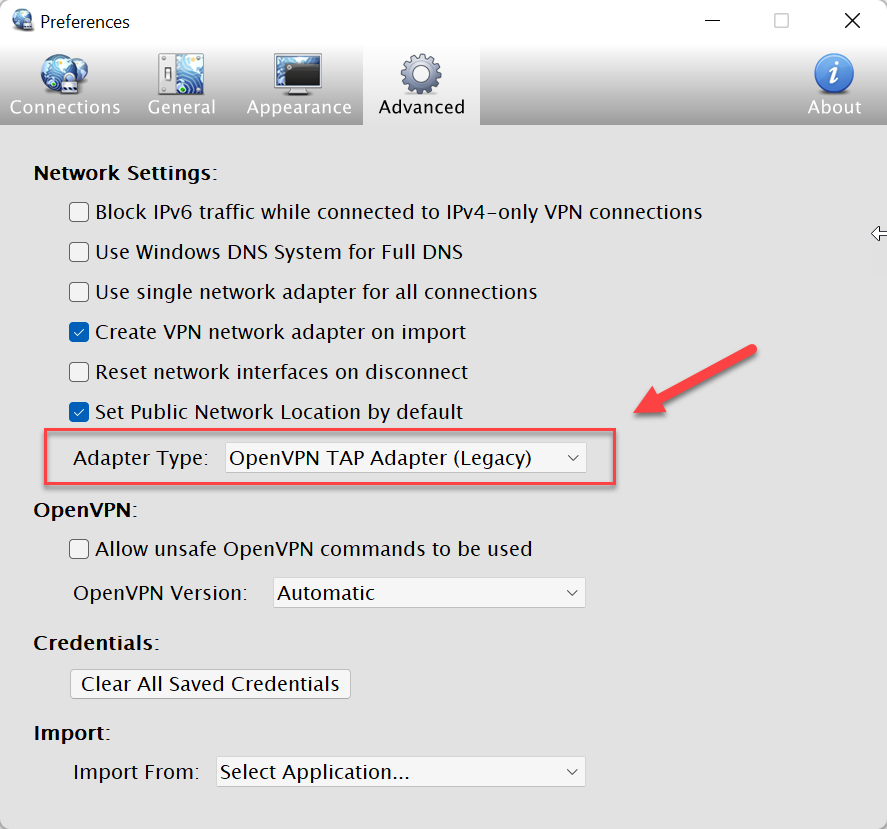
Note: If you are using Windows 11 – download and install the latest version of OpenVPN Connect (v3 or newer) and then in the Viscosity settings go to advanced settings and change the network adapter to “OpenVPN TAP Adapter (Legacy)”. This will allow the client to work for now.